Bring Trusted Industrial Data
to AI
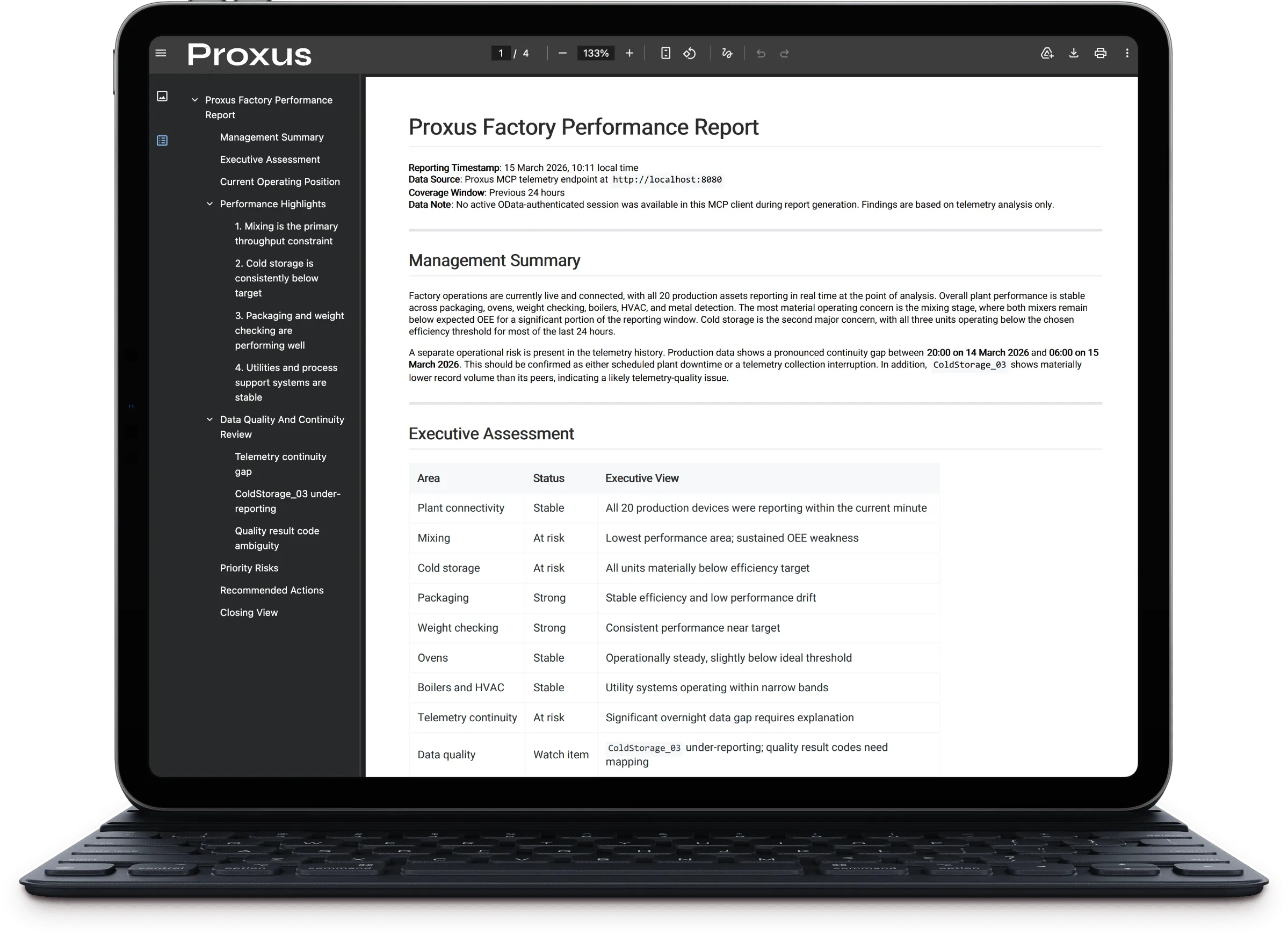
Connect approved assistants to operational data without opening control paths. Proxus MCP Server provides governed access to telemetry, operational entities, schema resources, and reusable prompts so AI can answer from real industrial context.
Why Proxus MCP Server?
MCP (Model Context Protocol) is the standard way to connect AI assistants to your systems. Proxus MCP Server provides a secure bridge to industrial data with strict scope controls. See how it works.
- Secure authentication, session-based access with audited login, expiry, and compatibility fallbacks.
- OData proxy, controlled access to Device, Tag, Rule, and Function entities.
- Telemetry querying, read-only ClickHouse access with injection protection.
- Schema discovery, tools plus MCP resources and templates for entities, telemetry, and protocol definitions.
- Reusable prompts, built-in MCP prompts for safe read, write, and telemetry investigation workflows.
- Governance, rate limiting, IP whitelisting, and full audit logging.
What stays protected
- No direct PLC/SCADA access
- No direct control-path writes or setpoint changes
- Governed access to telemetry, schema resources, and approved operational endpoints
- Outbound-only; no inbound control paths
- Auditability of queries and actions
How it works
Assistants connect through MCP. Proxus provides governed tools, schema resources, and reusable prompts for telemetry, operational entities, and metadata. You decide the scope. Read the MCP Server docs for setup steps.
- Select which tools, resources, prompts, entities, and time windows are visible.
- Assistants authenticate via MCP sessions; no direct DB credentials are shared.
- Visible operations still enforce `auth_required` or `auth_expired` at call time when needed.
- Telemetry, schema, and approved entity operations run under audit and RBAC controls.
- Optional business actions (tickets/notifications) go through approved endpoints, never direct OT control paths.
Allowed data paths
- Telemetry tools and safe SQL queries
- Schema resources like `proxus://schema/overview` and protocol templates
- Prompt-guided workflows for safe read, write, and telemetry analysis
- Governed entity access via OData and role-based visibility
Tools
Authentication, telemetry analysis, schema discovery, and governed OData operations.
Resources
Structured schema documents like platform overview, entity catalog, telemetry schema, and protocol templates.
Prompts
Reusable MCP workflows that steer assistants toward safe reads, controlled writes, and reliable telemetry investigations.
Use Cases
Give teams instant answers while keeping production safe and governed. Review FAQ for governance details.
Operations Q&A
Ask for current throughput, quality yields, or downtime reasons per line or shift.
Maintenance triage
Summarize recent faults and suggest the right work order in ERP/CMMS.
Energy & cost insight
Answer consumption and cost questions from telemetry without custom reports.
Shift handover
Generate concise summaries of alarms, stoppages, and KPIs for the next crew.
Security and governance
AI access is explicitly limited. You choose the data and time ranges; everything is logged.
- Scoped MCP surface, only the tools, resources, and prompts you expose are available to assistants.
- No credentials leak, assistants never receive DB passwords; access is proxied.
- Audit trails, discovery, queries, and approved actions are recorded for review.
- Call-time enforcement, visible operations can still return structured `auth_required` or `auth_expired` when access is not valid.
What AI can’t do
- No control writes or setpoint changes
- No direct PLC/SCADA connectivity
- No access outside approved telemetry/UNS scope
FAQ
Common questions on safety, data access, and governance.
No. Access is proxied through governed MCP surfaces; credentials are never shared.
No. Direct OT control writes are not exposed. Optional business actions can still be offered through governed endpoints such as ticketing or approved OData flows.
Choose which tools, resources, prompts, entities, time windows, and roles are exposed. Everything else stays invisible or is blocked at call time.
Yes. Queries and actions are logged for review.
The current MCP surface has been validated with Codex, Qwen, Claude-compatible workflows, Gemini CLI discovery, and MCP Inspector.
Ready to let your team talk to the factory safely?
Turn on governed AI access to telemetry, schema, and approved operational endpoints. Keep control logic isolated, keep answers fast.